The result of the authentication process may be used locally by the system performing the authentication or asserted elsewhere in a federated identity system. This document defines technical requirements …
Control: Implement mechanisms for authentication to a cryptographic module that meet the requirements of applicable laws, executive orders, directives, policies, regulations, standards, and …
Instead, regardless of the RMF risk level, the following rules apply for authentication to DoD unclassified and Secret Fabric networks, systems, applications, devices, information, or cloud...
- [PDF]
Authentication
Going from the basic obser-vation to a working, reliable authentication system is far from easy. But it can be made to work, to much the same extent as the other authentication mechanisms. We can use it, …
Electronic authentication (e-authentication) is the process of establishing confidence in user identities electronically presented to an information system. E-authentication presents a technical challenge …
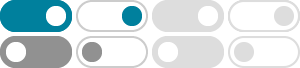
In order to perform the initial setup and configuration of Multi-Factor Authentication (MFA) on your account, please choose at least two of the following options:
Feb 25, 2026 · Overview This document is intended to serve as a reference for DFS ID users as they set up and use Multi-Factor Authentication (MFA).